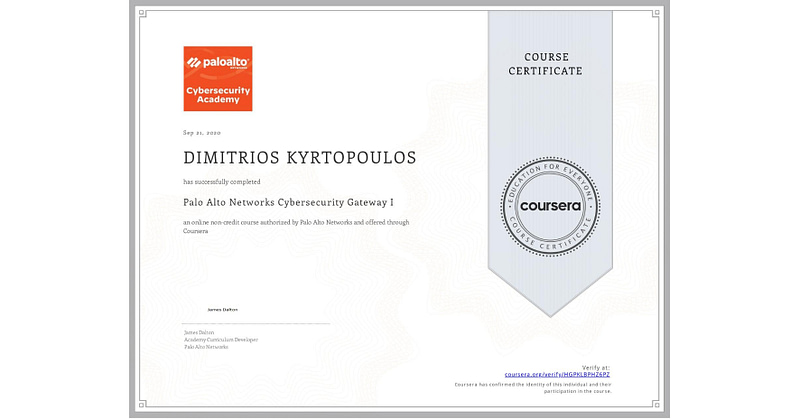
Palo Alto Networks Cybersecurity Gateway I
Instructor
About this Course
Gateway Part I provides the student with a partial understanding of the fundamental tenants of networking and covers the general concepts involved in maintaining a secure network computing environment. Upon successful completion of this course, students will be able to partially examine and describe general networking fundamentals, and also implement basic networking configuration techniques.
Why Should You Take This Course:
Gateway 1 Course Objectives:
Upon completion of this course, students will be able to:
• Demonstrate knowledge of interconnected technology in daily communication and understanding systems that need protection.
• Demonstrated knowledge of physical, logical, and virtual addressing that accommodates various sized networks through the use of subnet mask schemes.
• Explain the TCP/IP Model and correctly identify the functions of the specific layers including packet encapsulation and lifecycle.
Syllabus
Week 1: Gateway I: Course Home – Course Information
Begin your Gateway 1 experience here. Carefully evaluate the Course Information and Resources content area and identify the tools and processes you will use in this course. *** NEW LAB OS: All NDG labs are now utilizing Palo Alto Networks Firewall OS 9. Lab topics and activities are now performed on the Next Generation Firewall OS 9 platform.
Gateway I: Module 1 – Systems and Support
In this module you will examine how computing systems work within our Connected Globe, and how different work roles provide support and keep systems running properly.
Week 2: Gateway I: Module 2 – Networking and Network Devices
We all utilize a variety of different devices when connecting with Networking and Internetworking services. Module 3 looks at the devices, standards and services that are used to build and maintain network structures.
Week 3: Gateway I: Module 3 – PHYSICAL, LOGICAL AND VIRTUAL ADDRESSING
Network functionality and performance critically depends on address resolutions. Logical names, numbers and binary values are the addresses most commonly used to identify devices that are connected to a network. These addresses are evaluated by connected devices as they discover and map locations for both devices and network paths on Internal and External networks. You can understand how physical, logical and virtual addressing schemes need to be carefully designed.
Week 4: Gateway I: MODULE 4 – Network Models and Packet Encapsulation
The Internet is a packet-switched network comprised of hundreds of millions of routers and billions of servers and user endpoints. In a packet-switched network, devices share bandwidth on communications links to transport packets between a sender and receiver across a network. Packet encapsulation is the process of formatting packets from one network structure into another, for example from a wireless network to a wired network.
In order to understand the different network models and topologies you will need to have a fundamental knowledge of the Open Systems Interconnect – OSI – model, a basic understanding of how networking standards such as Ethernet 802.3 and WLAN 801.i, and understand how protocol standards such as TCP/IP define their specific frame structures for packets that are defined by a particular protocol, such as HTTP or FTP.